Security Center
Your privacy and security are our top priority
Our Mission
Your Security
Your privacy and the security of your personal information is important to us. We believe that informing our customers is the best way to protect them against identity theft and electronic fraud.
There are some simple steps that you can take to secure your information and drastically reduce your risk of falling victim to online threats. We recommend using all the following security tools to help protect your personal information anytime you are online. A properly protected computer provides for a safer online experience.
Cyber Security Information from our Blog
View the latest information from our blog about cyber security.
Protecting Your Account: New Zelle® Scams to Watch For
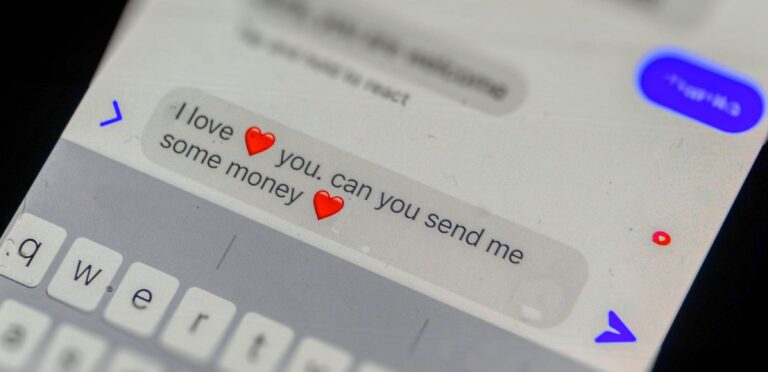
Sweet Talk to Financial Ruin: Romance Impostor Scams
Protect Yourself from Account Takeover Fraud: What You Need to Know
Security Alerts
June 28, 2024 - Fraud and scams are more prevalent than ever
BE ON THE LOOKOUT FOR FRAUD: Fraud and scams are more prevalent than ever
- Never log into your online banking because someone told you to.
- Never make a cash withdrawal because someone on the phone or online asked you to.
- Never wire or send funds to someone you have NOT met in person.
- The First will never call, text, or email you asking for your account information, debit card information, login, or password. If you initiated the call, you may be asked to verify confidential information, but never the other way around. If you receive a call from someone claiming to be from The First, hang up and contact us.
WE AT THE FIRST ARE HERE TO HELP. FEEL FREE TO CALL US AT 215-860-9100.
Our After-Hours Call Center (215-579-3401) is open 3:00-10:00 pm Monday–Friday
February 26, 2024 - Beware of Fraud Attempts
We have reports of a phishing scam that has been targeting bank customers. The suspicious text messages claim that your account is on hold. They contain numerous misspellings and punctuation errors. These messages are designed to trick you into revealing personal information or clicking on malicious links.
It’s crucial to stay vigilant and recognize the signs of phishing attempts. One common red flag is the presence of misspellings and grammatical errors in the messages. Legitimate communications from our bank are carefully crafted and thoroughly proofread, so any message containing noticeable errors should raise immediate suspicion.
Your security is our top priority, and we want to ensure that you feel confident and informed when it comes to protecting your financial information. If you receive any suspicious messages, emails, or calls claiming to be from our bank, please do not hesitate to contact your nearest branch immediately.
Remember, never provide personal or sensitive information in response to unsolicited communications, and always verify the legitimacy of any requests before taking action. By staying vigilant and cautious, we can work together to safeguard your accounts and financial well-being.
If you have any concerns or questions regarding the recent phishing scam or any other security-related matters, please don’t hesitate to reach out to us. We’re here to help you navigate through any challenges and ensure a safe banking experience for all our customers.
August 7, 2023 - Beware of Phishing Scams
This post is to inform you of a recent increase in phishing scams targeting our customers. Phishing is a fraudulent attempt to obtain your personal or financial information, such as passwords, account numbers, or credit card details, by pretending to be a legitimate entity. Phishing can occur through email, text message, phone call, or other means.
We urge you to be vigilant and protect yourself from these scams. Here are some tips to help you identify and avoid phishing:
– Do not open or respond to unsolicited emails or text messages that ask you to verify your account, update your information, or claim that there is a problem with your payment.
– Do not click on any links or attachments in suspicious emails or text messages. They may lead you to fake websites that look like ours, but are designed to steal your information.
– Do not provide any personal or financial information over the phone, unless you initiated the call and verified the identity of the person you are speaking to.
– Always check the sender’s address and the URL of the website you are visiting. Make sure they match our official domain name and email address.
– If you receive a phishing email or text message, please report it to us immediately by forwarding it to [email protected].
We take your security seriously and we are working hard to prevent and stop these scams. However, we cannot do it alone. We need your cooperation and awareness to keep your account safe.
Thank you for choosing The First and trusting us with your business.
May 31, 2022 - Intuit warns of QuickBooks phishing threatening to suspend accounts
Tax software vendor Intuit has warned that QuickBooks customers are being targeted in an ongoing series of phishing attacks impersonating the company and trying to lure them with fake account suspension warnings.
Today’s alert comes after Intuit received multiple user reports who received these phishing emails and notified their QuickBooks accounts were suspended following a failed business info review.
“We’re writing to let you know that after conducting a review of your business, we have been unable to verify some information on your account. For that reason, we have put a temporary hold on your account,” the attackers say in the phishing messages while impersonating the QuickBooks support team.
“If you believe that we’ve made a mistake, we’d like to remedy the situation as quickly as possible. To help us effectively revisit your account please complete the below verification form. Once verification has been completed, we will re-review your account within 24-48 hours.”
Clicking the “Complete Verification” button in the phishing email will likely redirect the recipients to a landing phishing site designed to harvest their personal information or infect their systems with malware.
The accounting software maker also added that the sender “is not associated with Intuit, is not an authorized agent of Intuit, nor is their use of Intuit’s brands authorized by Intuit.”
How to make sure you’re not phished
Intuit advises customers who received one of these phishing messages not to click any embedded links or open attachments.
It also recommends deleting them from the inbox to avoid getting infected with malware or sent to some phishing landing page under the attacker’s control that would attempt to harvest the targets’ credentials.
QuickBooks users who have already opened attachments or clicked links after receiving one of these phishing emails should:
- Delete any downloaded files immediately.
- Scan their systems using an up-to-date anti-malware solution.
- Change their passwords.
Intuit also provides detailed info on how customers can protect themselves from phishing attempts on its support website.
Earlier this year, in February, Intuit warned QuickBooks customers they were the targets of a phishing campaign impersonating the company and threatening to delete their accounts.
September 23, 2021 - Reducing the Risk of Fraud on the Zelle Network®
The First National Bank and Trust Co. of Newtown actively works to reduce the risk of fraud on the Zelle Network®, however, the recent health concerns that have impacted every aspect of our lives have led consumers to increasingly turn to digital payments, enabling fraudsters to hide among the larger volume. These fraudsters are taking advantage of the pandemic, using fear and uncertainty to victimize consumers.
The purpose of this bulletin is to notify you of a social engineering scam that has been observed across multiple social payment applications, including Zelle®, and to remind you of the need for continued vigilance to protect your Zelle® account.
Social Engineering Scam
In one scenario, the consumer receives a text from a fraudster to alert about a suspicious transaction. Upon receiving a response text declining the transaction from the consumer, the fraudster calls the consumer, pretending to be the fraud department of the financial institution. The fraudster gains access to the consumer’s online banking account by requesting the username and one-time password, which is then used to reset the password. Upon gaining access to the online account, the fraudster registers for Zelle® and attempts to send payments.
In most of these cases, our risk models detect the fraud activity and the transactions as high risk. The user then receives a stepped-up authentication request via SMS (text) to authorize the payment. Through social engineering and direct calls, some users are still falling victim to these fraud scams. In these cases, the fraudster calls to convince the consumer to authorize the stepped-up authentication request, so that the consumer can receive a refund from the previously fraudulent transaction. In reality, the consumer is not getting a refund, but is sending the payment to the fraudster.
Remember:
FNBN will never call you to request information you received via text (SMS) or pressure you to reset your online banking log in password
Don’t trust caller ID; Caller ID may be modified to show FNBN’s name
Don’t provide your online banking log in credentials, one-time password, account number or personal information by email or text or phone call. Instead, reach out to FNBN to confirm that the request is legitimate by calling us at 215-860-9100
Don’t give information over the phone if you receive a call stating that a transaction is canceled, even if the caller claims to be from FNBN. Once again, contact us directly by phone at 215-860-9100 to inquire about the transaction
Don’t click on links in unsolicited emails or texts
Don’t give an unsolicited caller remote access to your computer
New Text Message Scam
New Credit Card Scam
The callers do not ask for your card number; they already have it. This information is worth reading. By understanding how the VISA & Master Card Telephone Credit Card Scam works, you’ll be better prepared to protect yourself.
One of our employees was called on Wednesday from ‘VISA’, and I was called on Thursday from ‘Master Card’.. The scam works like this: Caller: ‘This is (name), and I’m calling from the Security and Fraud Department at VISA. My Badge number is 12460. Your card has been flagged for an unusual purchase pattern, and I’m calling to verify. This would be on your VISA card which was issued by (name of bank). Did you purchase an Anti-Telemarketing Device for $497.99 from a Marketing company based in ?’
When you say ‘No’, the caller continues with, ‘Then we will be issuing a credit to your account. This is a company we have been watching and the charges range from $297 to $497, just under the $500 purchase pattern that flags most cards. Before your next statement, the credit will be sent to (gives you your address), is that correct?’
You say ‘yes’. The caller continues – ‘I will be starting a Fraud investigation. If you have any questions, you should call the 1- 800 number listed on the back of your card (1-800 -VISA) and ask for Security.’
You will need to refer to this Control Number. The caller then gives you a 6 digit number. ‘Do you need me to read it again?’
Here’s the IMPORTANT part on how the scam works. The caller then says, ‘I need to verify you are in possession of your card’. He’ll ask you to ‘turn your card over and look for some numbers’. There are 7 numbers; the first 4 are part of your card number, the next 3 are the security Numbers that verify you are the possessor of the card. These are the numbers you sometimes use to make Internet purchases to prove you have the card. The caller will ask you to read the 3 numbers to him. After you tell the caller the 3 numbers, he’ll say, ‘That is correct, I just needed to verify that the card has not been lost or stolen, and that you still have your card. Do you have any other questions?’ After you say No, the caller then thanks you and states, ‘Don’t hesitate to call back if you do, and hangs up.
You actually say very little, and they never ask for or tell you the Card number.. But after we were called on Wednesday, we called back within 20 minutes to ask a question.. Are we glad we did! The REAL VISA Security Department told us it was a scam and in the last 15 minutes a new purchase of $497.99 was charged to our card.
Long story – short – we made a real fraud report and closed the VISA account. VISA is reissuing us a new number. What the scammers want is the 3-digit PIN number on the back of the card Don’t give it to them. Instead, tell them you’ll call VISA or Master card directly for verification of their conversation. The real VISA told us that they will never ask for anything on the card as they already know the information since they issued the card! If you give the scammers your 3 Digit PIN Number, you think you’re receiving a credit. However, by the time you get your statement you’ll see charges for purchases you didn’t make, and by then it’s almost too late and/or more difficult to actually file a fraud report.
FBI Warns of Rise in Phone-Based Scams
New threat: Phishing attempts that ask the victim to call their bank to reactivate a credit card, then provide a false phone number.
With consumers finally getting wise to phishing attacks, scammers are hitting the phones.
The U.S. Federal Bureau of Investigation’s Internet Crime Complaint Center (IC3) warned Thursday that so-called “vishing” attacks are on the rise. These are scams where criminals send an e-mail or text message to a victim, saying there has been a security problem and the victim needs to call his or her bank to reactivate a credit or debit card.
“Upon calling the telephone number, the recipient is greeted with ‘Welcome to the bank of …’ and then [is] requested to enter their card number in order to resolve a pending security issue,” the IC3 said in its alert.
In the past few years, inexpensive VoIP (Voice over Internet Protocol) technology and open-source call-center software has made it inexpensive for scammers to set up phony call centers, paving the way for these new types of scams. Security experts say that vishing can be more effective than traditional phishing techniques — which direct victims to fake Web sites — because the voice-based attacks have not been as widely publicized.
A new vishing scam involves sending text messages to cell phones, instructing victims to contact the fake online bank to renew their accounts, the IC3 said.
Those who are unsure whether they have been targeted by this scam should look up the bank’s phone number and call the bank directly, the IC3 advises.
Operated in partnership with the FBI and the National White Collar Crime Center, the IC3 is a clearing house for Internet crime complaints.
Pretext Calling and Identity Theft.
Pretext calling is a fraudulent means of obtaining an individual’s personal information. Pretext callers may contact financial institution employees, posing as their customers, in order to access customers’ personal account information. These callers may also contact consumers at home, posing as employees from a financial institution. Information obtained from pretext calling may be sold to debt collection services, attorneys, and private investigators for use in court proceedings. Identity thieves may also engage in pretext calling to obtain personal information for use in creating fraudulent accounts.
Steps you should take to protect yourself against identity theft and pretext calling include:
Do not give personal information, such as account numbers or social security numbers, over the telephone, through the mail, or over the Internet unless you initiated the contact or know with whom you are dealing.
Store personal information in a safe place and tear up old credit card receipts, ATM receipts, old account statements, and unused credit card offers before throwing them away.
Protect your PINs and other passwords. Avoid using easily available information like your mother’s maiden name, your birth date, the last four digits or your social security number, your phone number, etc.
Carry only the minimum amount of identifying information and the number of credit cards that you need.
Pay attention to billing cycles and statements. Inquire of the bank if you do not receive a monthly bill; it may mean the bill has been diverted by an identity thief.
Check account statements carefully to ensure all charges, checks, or withdrawals were authorized.
Guard your mail from theft. If you have the type of mailbox with a flag to signal the box contains mail, do not leave bill payment envelopes in your mailbox with the flag up. Instead, deposit them in a post office collection box or at the local post office. Promptly remove incoming mail.
Order copies of your credit report from each of the three major bureaus once a year to ensure they are accurate. (A fee may apply)
If you prefer not to receive pre-approved offers of credit, you can opt out of such offers by calling 1-888-5-OPT OUT.
If you want to remove your name from many national direct mail lists, send your name and address to:
DMA Mail Preference Service
P.O. Box 9008
Farmingdale, NY 11735-9008
If you want to reduce the number of telephone solicitations from many national marketers, send your name, address and telephone number to:
DMA Telephone Preference Service
P.O. Box 9014
Farmingdale, NY 11735-9014
Banking Department Urges Caution when Cashing Cashier's Checks from People You Don't Know
There have been an increasing number of Pennsylvanians reporting that they are being defrauded by counterfeit cashier’s checks.
In general, the fraud unfolds like this: A consumer is part of a fairly large financial transaction with someone who generally says that they live outside of the United States. The types of transactions that have been reported include payments for large items purchased through online auctions, deposits for apartments, and fees for nanny services, for example.
The so-called “buyer” sends an official-looking cashier’s check to pay for the service. The consumer, then, takes the check to the bank and cashes it.
There are two ways the scam can unfold: In the first, the buyer sends a check for well over the amount of the purchase (with some excuse about why) and asks the consumer to immediately refund the difference once they’ve cashed the check. In the second, the buyer waits a day or two (but only a very short time) and makes some excuse for canceling the transaction and asks the consumer to wire all of the money back.
A similar scam suggests that the consumer has ”won” a lottery or other prize but must send some of the proceeds of the check back for some specific reason, like processing or taxes.
The counterfeit cashier’s checks are such good reproductions that they’re difficult to spot, even by experienced financial professionals. Despite the fact that the consumer’s bank cashes the check, it will not be honored when the bank presents it to the ”issuing” institution for payment. The bank then, requires the consumer to return the funds.
The problem is that, by the time the fraudulent check works its way through the banking system (which can sometimes take more than 30 days), the con-artist has already taken the consumer’s money.
You can protect yourself by:
- understanding that when cashing a cashier’s check, even though the bank has provided you with the money, you are responsible for the funds until your bank has received the proceeds from the institution which originally issued the check
- being cautious of transactions with people you don’t know who purchase items via cashier’s check
- avoiding any situation where someone pays more than the purchase price of an item and demands that the extra money be returned
- being suspect of any cashier’s check that just shows up in the mail, especially if it has a ”congratulations” letter attached
- holding any funds provided by cashier’s check from someone you don’t know for 30 – 45 days before using those fund, especially when you have any sense that the transaction is out of the ordinary
If you believe that you’ve been the victim of this type of scam, please call the Pennsylvania Attorney General’s office at (800) 441-2555, the U.S. Secret Service at (202) 406-5850, or the Pennsylvania Department of Banking at (800) PA BANKS.
FBI Fraud Alert Questionnaire
Fraudulent Emails Requesting Personal Information
Recently, many Americans have received a series of fraudulent e-mails, which direct recipients to websites where they are asked to verify sensitive personal information. The e-mails claim that the individual’s personal information is necessary to assist in the fight against terrorism or for some other purpose supposedly required by law. These e-mails are purportedly sent from several government agencies or include content related to government agencies including the Federal Deposit Insurance Corporation, the Office of the Comptroller of the Currency, the Securities Investor Protection Corporation and others. The websites to which the email recipients are directed are often very similar to, if not actual clones of official government sites.
The fraudulent e-mails are part of a scam known as “phishing.” Phishing is the fraudulent scheme of sending an e-mail to a user falsely claiming to be a legitimate company. The email attempts to con the user into surrendering private information that could later be used for identity theft. The e-mail directs the user to visit a Web site where they are asked to update personal information, such as name, account and credit card numbers, passwords, social security numbers and other information. The Web site, however, is bogus and set up only to steal the user’s information.
As part of the Treasury Department’s efforts to fight identity theft, we want to assure Americans that federal financial agencies do not communicate with consumers by e-mail requesting important personal information such as your name, account numbers, date of birth and social security number.
Consumers can protect themselves from this latest identity theft scam by following these useful tips, which were developed by the Federal Trade Commission:
- If you get an email that warns you, with little or no notice, that an account of yours will be shut down unless you reconfirm your billing information, do not reply or click on the link in the email. Instead, contact the company cited in the email using a telephone number or Web site address you know to be genuine.
- Avoid emailing personal and financial information. Before submitting financial information through a Web site, look for the “lock” icon on the browser’s status bar. It signals that your information is secure during transmission.
- Review credit card and bank account statements as soon as you receive them to determine whether there are any unauthorized charges. If your statement is late by more than a couple of days, call your credit card company or bank to confirm your billing address and account balances.
- Report suspicious activity to the FTC. Send the actual spam to [email protected]. If you believe you’ve been scammed, file your complaint at www.ftc.gov, and then visit the FTC‘s identity theft web site (www.ftc.gov/idtheft) to learn how to minimize your risk of damage from identity theft.
The Treasury and federal financial regulators are working hard to combat identity theft including the use of new tools in legislation recently signed by President Bush. But all consumers must take reasonable precautions in the use of their personal financial information in order to help prevent themselves from becoming victims of identity thieves.
ATM Safety Tips: When Using An ATM…
- Be aware of your surroundings, particularly at night.
- Consider having someone accompany you when using the ATM after dark.
- If you observe or sense suspicious persons nearby, do not use the ATM at that time. Or, if you are in the middle of a transaction, cancel the transaction. Leave the area and come back another time or use an ATM at another location.
- If you are approached by any person who asks you to do them a “favor” or tries to draw you into conversation, cancel your transaction and leave the area. Report the incident to us as soon as possible.
- When using the ATM at night, park close to the ATM in a well-lighted area and always lock your car.
- If the lights on or around an ATM are not working, don’t use it. Report it to us the next day.
- If you are using another financial institution’s ATMs and shrubs or trees block the view, select another ATM.
- If you are using a drive-up ATM, be sure passenger windows and doors are locked.
- To keep your account information confidential, always take your receipts with you.
- Don’t display any cash. As soon as you complete the transaction, pocket the money and count it later.
- Report all crimes to the police immediately.
- If your card is lost or stolen, report it to us immediately. Call 215-579-3400 Monday-Friday 8:30 am to 5:00 pm or 800-236-2442 after business hours.
- Be careful not to reveal your secret code (PIN). When you punch it in, use your body to “shield” the keyboard. Don’t carry your personal identification number with your card, and never attach it to your card.
Copyright © 1992 Bankers’ Hotline.
Originally appeared in Bankers’ Hotline, Vol. 2, No. 11, 2/92
If you have any questions about these security and fraud alerts, please feel free to contact the bank at 215-860-9100.
Security
Online Protection
Guard Your Personal Information
Since you can control the information you choose to release, you are the best person to protect your personal information. There are some easy ways to do this by keeping anything with any personal or account information in a safe place, providing your information only to trusted sources, and reducing the amount of mail you receive with your information on it.
It is okay to be skeptical when providing your personal information. If you can’t verify the legitimacy of the business or person that you may be providing your information to, or if you do not understand why a certain piece of information is needed, you may want to think twice about giving out the information. More Information on Guarding Your Personal Information.
The First National Bank & Trust Company employees will never call and ask for digital banking log in credentials.
Secure Your Computer
You do not have to be an expert in computers to protect yourself on the Internet from online fraud and identity theft.
You should install anti-spyware, anti-virus, and a personal firewall on your computer. There are many of these products available that will help you prevent criminals from gaining access to your computer and stealing your personal information. Some are even available free of charge. A properly protected computer will provide you with secure access to your online information and combat the efforts of criminals trying to gain access to your accounts.
Understanding what online threats exist is always helpful too, but there are other steps that you can easily take to further reduce your fraud and identity theft risk while online. More Information on Securing Your Computer.
Security
Protecting Your Account
Take care of your personal information
- Carry only necessary identification with you. Don’t carry your Social Security card.
- Treat your credit cards, debit cards and checks like cash.
- Retrieve incoming mail from your mailbox quickly. Do not leave outgoing mail in an unsecured mailbox or any other location or switch to paperless statements if possible.
- Make copies of all of the financial information that you carry with you daily and store the copies in a safe place.
Provide information only to trusted sources
- Never provide personal information unless you have initiated the contact and have confirmed the business or person’s identity.
- Be cautious of telephone and door-to-door solicitations.
- Be skeptical of offers that seem “too good to be true”. They usually are.
Spam Email
Spam is the electronic equivalent of junk mail. The term refers to unsolicited, bulk – and often unwanted – email. Here are ways to reduce spam:
- Enable filters on your email programs: Most ISPs (Internet Service Providers) and email providers offer spam filters. However, depending on the level you set, you may wind up blocking emails you want. It’s a good idea to occasionally check your junk folder to ensure the filters are working properly.
- Report spam: Most email clients offer ways to mark an email as spam or report instances of spam. Reporting spam will also help to prevent the messages from being directly delivered to your inbox.
- Own your online presence: Consider hiding your email address from online profiles and social networking sites or only allowing certain people to view your personal information.
Phishing Email
Phishing attacks use email or malicious websites (clicking on a link) to collect personal and financial information or infect your machine with malware and viruses. Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
Spear Phishing Email
Spear phishing is highly specialized attacks against a specific target or small group of targets to collect information or gain access to systems.
For example, a cybercriminal may launch a spear phishing attack against a business to gain credentials to access a list of customers. From that attack, they may launch a phishing attack against the customers of the business. Since they have gained access to the network, the email they send may look even more authentic and because the recipient is already a customer of the business, the email may more easily make it through filters and the recipient may be more likely to open the email.
The cybercriminal can use even more devious social engineering efforts such as indicating there is an important technical update or new lower pricing to lure people.
Phone Scams
Phone scams are no joke. Scammers target millions of Americans every year via robo dialers and many people fall victim as they are threatened with arrest warrants or guaranteed free vacations.
Typical phone scams often involve free vacations and prizes, computer hacking and repair services, scams involving loans, phony debt collectors, fake charities, medical alert/scams targeting seniors, warrant threats and IRS calls.
Phone calls from criminals impersonating IRS agents remain an ongoing threat to taxpayers. The IRS has seen a surge of these phone scams in recent years as scam artists threaten taxpayers with police arrest, deportation and license revocation, among other things.
Quick Tips
When in doubt, throw it out: Links in email, tweets, posts and online advertising are often how cybercriminals try to compromise your information. If it looks suspicious, even if you know the source, it’s best to delete or, if appropriate, mark it as junk.
Think before you act: Be wary of communications that implores you to act immediately, offers something that sounds too good to be true or asks for personal information.
Make your password a sentence: A strong password is a sentence that is at least 12 characters long.
Unique account, unique password: Having separate passwords for every account helps to thwart cybercriminals. At a minimum, separate your work and personal accounts and make sure that your critical accounts have the strongest passwords.
Get two steps ahead: Turn on two-step authentication – also known as two-step verification or multi-factor authentication – on accounts where available. Two-factor authentication can use anything from a text message to your phone to a token to a biometric like your fingerprint to provide enhanced account security.
Pay attention to the website’s URL: Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com versus .net).
Keep a clean machine: Having the latest operating system, software, web browsers, anti-virus protection and apps are the best defenses against viruses, malware, and other online threats.
Security
Protect Your Personal Information
Take Care of Your Personal Information
- Carry only necessary identification with you. Don’t carry your Social Security card.
- Treat your credit cards and Debit Cards like cash.
- Retrieve incoming mail from your mailbox quickly. Do not leave outgoing mail in an unsecured mailbox or any other location.
- Make copies of all of the financial information that you carry with you daily and store the copies in a safe place.
Provide Information Only to Trusted Sources
- Never provide personal information unless you have initiated the contact and have confirmed the business or person’s identity.
- Be cautious of telephone and door-to-door solicitations.
- Be skeptical of offers that seem “too good to be true”. They usually are.
- Learn to recognize fraudulent emails. More information
Security
Identity Theft
Causes of Identity Theft
Dumpster Diving
Mail Theft
ATM Theft, Skimming
Imposters
Direct Access to Personal Documents in the Home
Purse/Wallet Theft
Prevent Identity Theft
- Secure your social security number. Don’t carry your social security card in your wallet or write your number on your checks. Only give out your social security number (SSN) when absolutely necessary.
- Don’t respond to unsolicited requests for personal information (your name, birthdate, social security number, or bank account number) by phone, mail, or online.
- Watch out for “shoulder surfers.” Shield the keypad when typing your passwords on computers and at ATMs.
- Collect mail promptly. Ask the post office to put your mail on hold when you are away from home.
- Pay attention to your billing cycles. If bills or financial statements are late, contact the sender.
- Review your receipts. Ask for carbon copies and incorrect charge slips as well. Promptly compare receipts with account statements. Watch for unauthorized transactions.
- Shred receipts, credit offers, account statements, and expired cards, to prevent “dumpster divers” from getting your personal information.
- Store personal information in a safe place at home and at work.
- Install firewalls and virus-detection software on your home computer.
- Create complex passwords that identity thieves cannot guess easily. Change your passwords if a company that you do business with has a breach of its databases
- Order your credit report once a year and review to be certain that it doesn’t include accounts that you have not opened. Check it more frequently if you suspect someone has gained access to your account information.
Security
Business Security Tips
Business E-mail Compromise scam (BEC)
Establish cyber security rules for your employees
Protect against viruses, spyware, malware and other malicious code such as Ransomware
Educate employees about safe social media practices
Manage and assess risk
Download and install software updates when they are available
Make backup copies of important business data and information
Control physical access to computers and network components
Secure Wi-Fi networks
Passwords Are Essential
The first suggestion is to “Create unbreakable passwords” for accounts related to your online presence, such as the domain registrar, hosting account, SSL provider, social media, and PayPal. While there is a lot of discussion about the need for better authentication schemes, passwords are still the main way to protect online accounts, making strong passwords essential.
Criminals can easily set up computers to cycle through random combinations to brute-force attacks. If the password is weak, this process takes very little time. A password manager is recommended to randomly generate strong passwords and to store them securely. If the service offers two-factor authentication, you should really take advantage of the extra layer of protection.
Website – Scan Your Sites
Website – Update & Patch
Website – SSL Certificates
Website – Don’t Lose Control
Security
Securing Your Computer & Network
Anti-Virus Protection
Anti-Malware protection
- Anti-malware software has become just as popular as Anti-Virus software. Spyware, viruses, worms and trojans are all malicious programs that are loaded onto your computer without your knowledge and commonly referred to as malware. Whether the goal of these programs is to capture or destroy information, to attack other computers or to swamp your computer with advertising, you don’t want them. Scammers are sneaky as they will disguise malware as an email from a friend or useful website.
- Viruses and worms spread by infecting computers and then replicating. Spyware and trojans disguise themselves as a legitimate application and embed themselves into your computer, to monitor your activity, collect information and deliver it back to online criminals. All are serious threats to the security of your computer.
Firewall
Operating System and Software Updates
Activate a Pop-up Blocker
Browsing the web safely
Change the name of your home router
Change the pre-set password on your router
Protect all devices that connect to the Internet
Plug & scan
Back it up
Recycle your old hardware properly
Security
Mobile Phone Protection
Regularly update your device
Enable encryption
Use a passcode
Do not use public Wi-Fi
Install applications from trusted sources
Install a phone locator/remote erase app
Disable unwanted services when not in use
Bluetooth and Near Field Capabilities (NFC) can provide an easy way for an unauthorized user nearby to gain access to your data. Turn these features off when they are not required.
Carefully dispose of mobile devices
Security
Vacation Security Tips
Home Alone
Stolen “Keys”
Missed Connection
- Some cyber criminals specialize in “sniffing” the Wi-Fi and public networks in airports and coffee shops, allowing the criminal to collect and read all information sent over a wireless network.
- Other criminals use a practice called “juice jacking”, where the criminal rigs a public charging kiosk to siphon information directly from your device when you plug into it.
Who’s the Boss?
When in Rome…
Easy Tips to Protect Yourself
- Use discretion when posting personal information on social media. This information is a treasure-trove to social engineers. Do not post information about travel plans or details; save the pictures and updates until after you return home.
- Set email away messages to only respond to known contacts in your address book.
- Disable geo-locational features, such as automatic status updates and friend finder functionalities.
- Remind friends and family members to exercise the same caution.
Easy Tips to Protect Your Devices
- Keep your electronic devices with you at all times.
- Before traveling abroad, change all passwords that you will use while traveling, and upon return change the passwords of any accounts that were accessed while abroad. This includes passwords used by social media websites and email providers, for which you have automatic logins.
- Do not access sensitive accounts (e.g. banks, credit cards, etc.) or conduct sensitive transactions over public networks, including hotel and airport wi-fi and business centers, or Internet cafés.
- Use up-to-date anti-virus, anti-spyware, and anti-adware protection software; apply recommended patches to your operating system and software.
- Use wired connections instead of Bluetooth or Wi-Fi connections, whenever possible.
- Do not plug USB cables into public charging stations; only connect USB powered devices using the intended AC power adapter.
- Know the local laws regarding online behavior, as some online behaviors are illegal in certain countries.